Supported Cipher Suites
A Cipher Suite is a set of cryptographic algorithms. The schannel SSP implementation of the TLS or SSL protocols uses algorithms from a cipher suite to create keys and encrypt information. It is important to have secure communication between the client and the server.
Pulse supports the following cipher suites when it connects to the server. The server must support a minimum TLSv1.2 version.
- TLS_ECDHE_ECDSA_WITH_RC4_128_SHA
- TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA
- TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA
- TLS_ECDHE_RSA_WITH_RC4_128_SHA
- TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
- TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256
- TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256
Ciphers not supported in Pulse
The “RSA key exchange” Cipher Suites differ significantly from ECDHE cipher suites. Instead of signing an ephemeral key exchange, they encrypt the session key with the certificate’s public key. This method has two disadvantages:
- No Forward Secrecy: If the certificate key is compromised, all the past and future connections can be decrypted.
- Vulnerability to Padding Oracle Attacks: The server must decrypt attacker-provided cipher texts with the certificate’s private key in constant time to prevent padding Oracle attacks. However, there are concerns that current methods, such as the rsa.DecryptPKCS1v15SessionKey API might not be fully secure against such attacks, as highlighted by the Marvin attack.
As part of the CVE fixes, Pulse does not support the following RSA ciphers:
- TLS_RSA_WITH_AES_128_GCM_SHA256
- TLS_RSA_WITH_AES_256_GCM_SHA384
- TLS_RSA_WITH_AES_128_CBC_SHA
- TLS_RSA_WITH_AES_256_CBC_SHA
- TLS_RSA_WITH_3DES_EDE_CBC_SHA
Troubleshooting
The server is not accepting connections
- Identify Ciphers that support the server. Also, ensure that the server supports TLSv1.2.
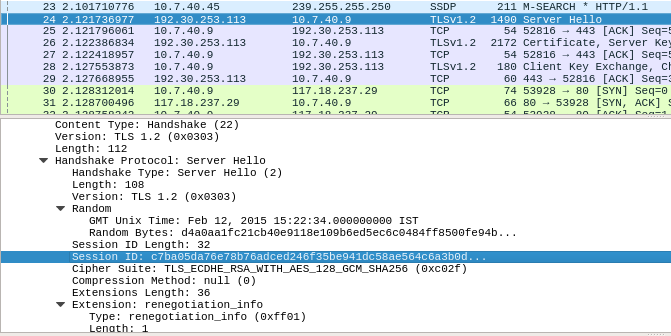
- Take TCPDump of the request and identify if the TLS handshake was successful. Ideally, it must have Client Hello, Server Hello, and Certificate or Key exchange. Check what Cipher suite was used in Client Hello and check if the server supports that cipher suite.
Unable to log on to the Pulse UI via LDAP
If you are unable to log on to the Pulse UI via LDAP, and the LDAP server only supports the ciphers deprecated by Pulse, Acceldata can temporarily reenable the required ciphers.
In the ad-ldap service, add the following environment variable:
GODEBUG=tlsrsakex=1This approach is not recommended and the LDAP server must be configured to support the cipher suites provided above.