Documentation
ODP 3.3.6.4-1
Release Notes
What is ODP
Installation
Component User guide and Installation Instructions
Upgrade Instructions
Downgrade Instructions
Reference Guide
Security Guide
Troubleshooting Guide
Uninstall ODP
Title
Message
Create new category
What is the title of your new category?
Edit page index title
What is the title of the page index?
Edit category
What is the new title of your category?
Edit link
What is the new title and URL of your link?
Install Knox
Summarize Page
Copy Markdown
Open in ChatGPT
Open in Claude
Connect to Cursor
Connect to VS Code
Install Knox
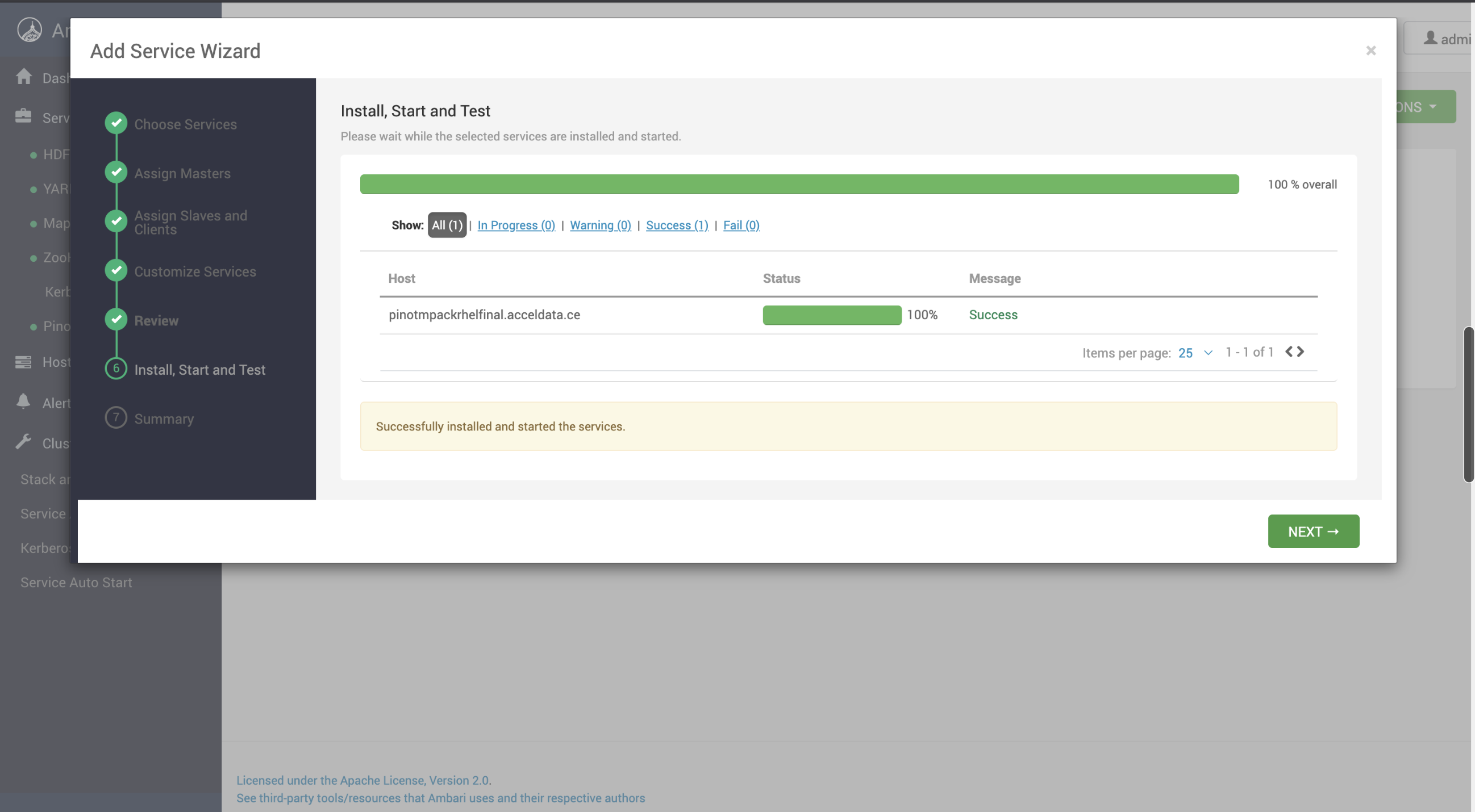
Perform the following steps to install Knox.
- Install the Knox service from the Ambari UI.
- Add entry for the Pinot service in the topology.
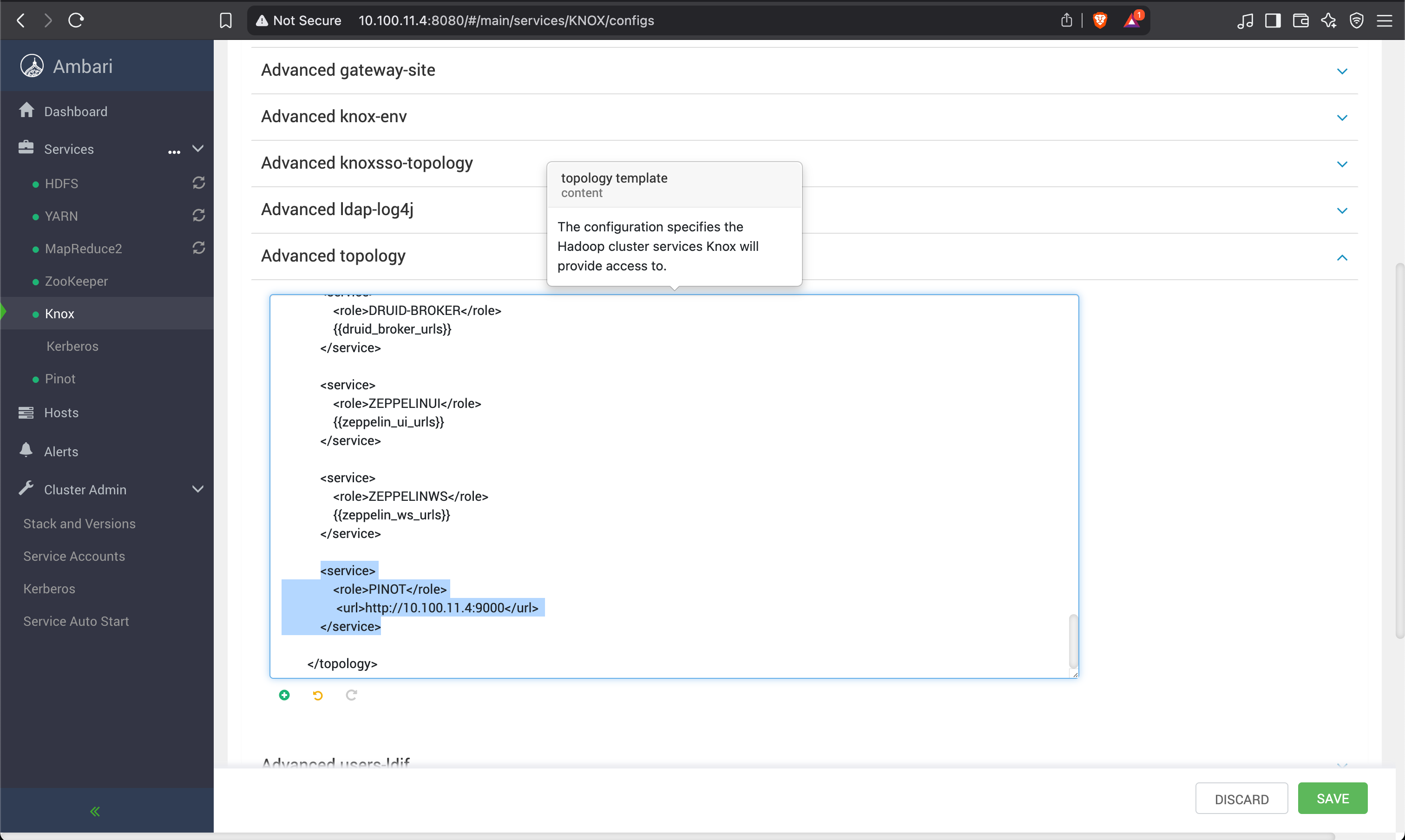
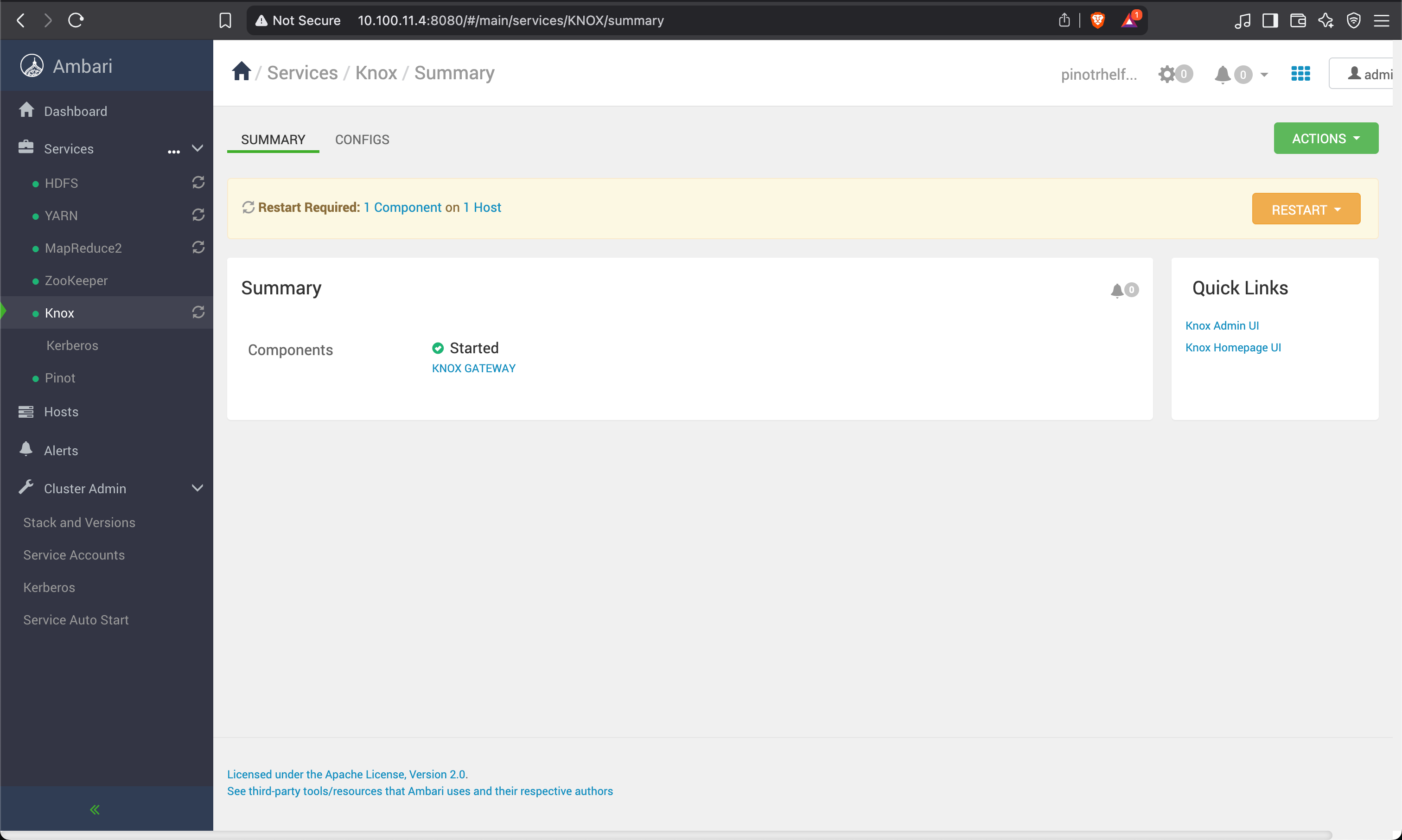
- Save and restart Knox.
Start the demo LDAP Server
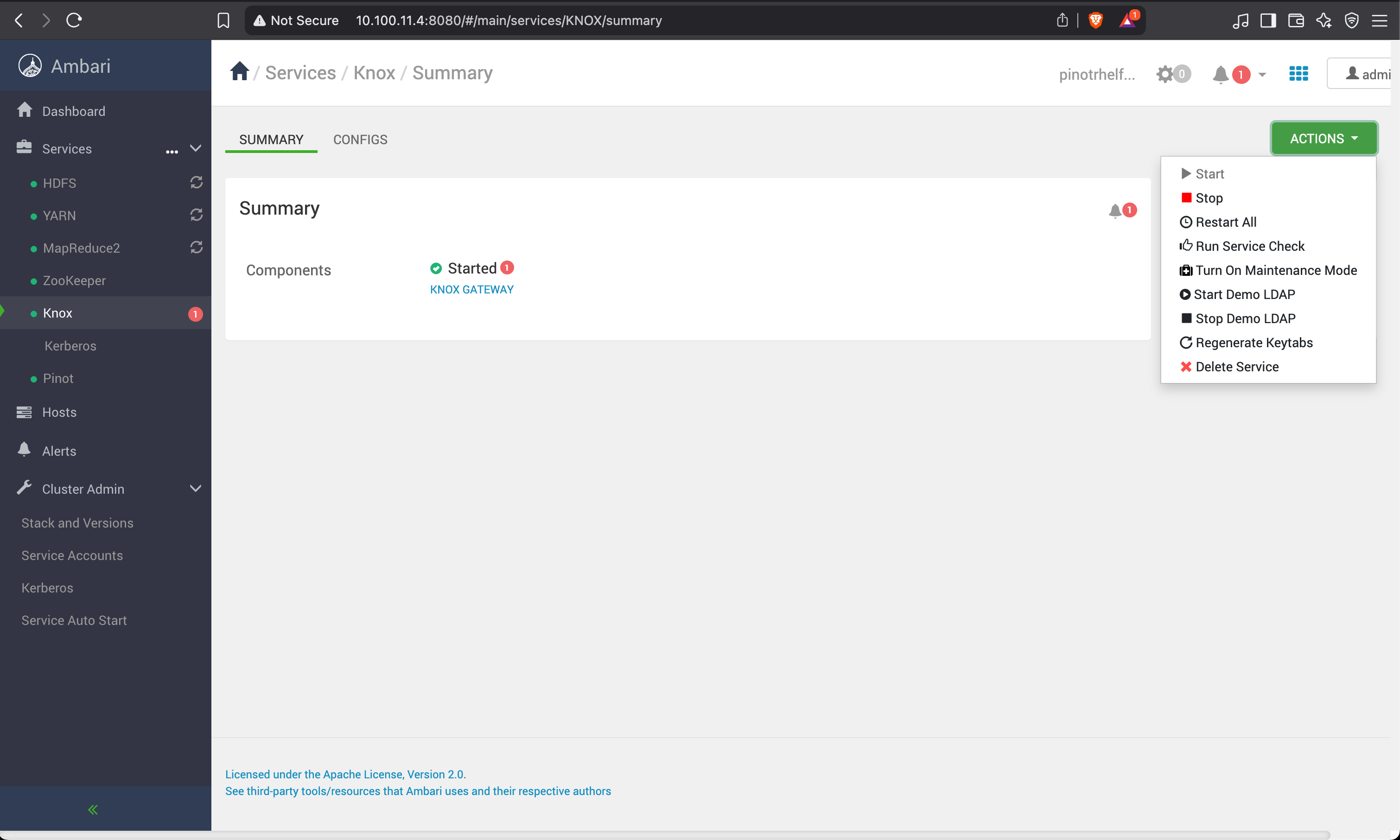
If you are enabling Knox, disable the basic auth option.
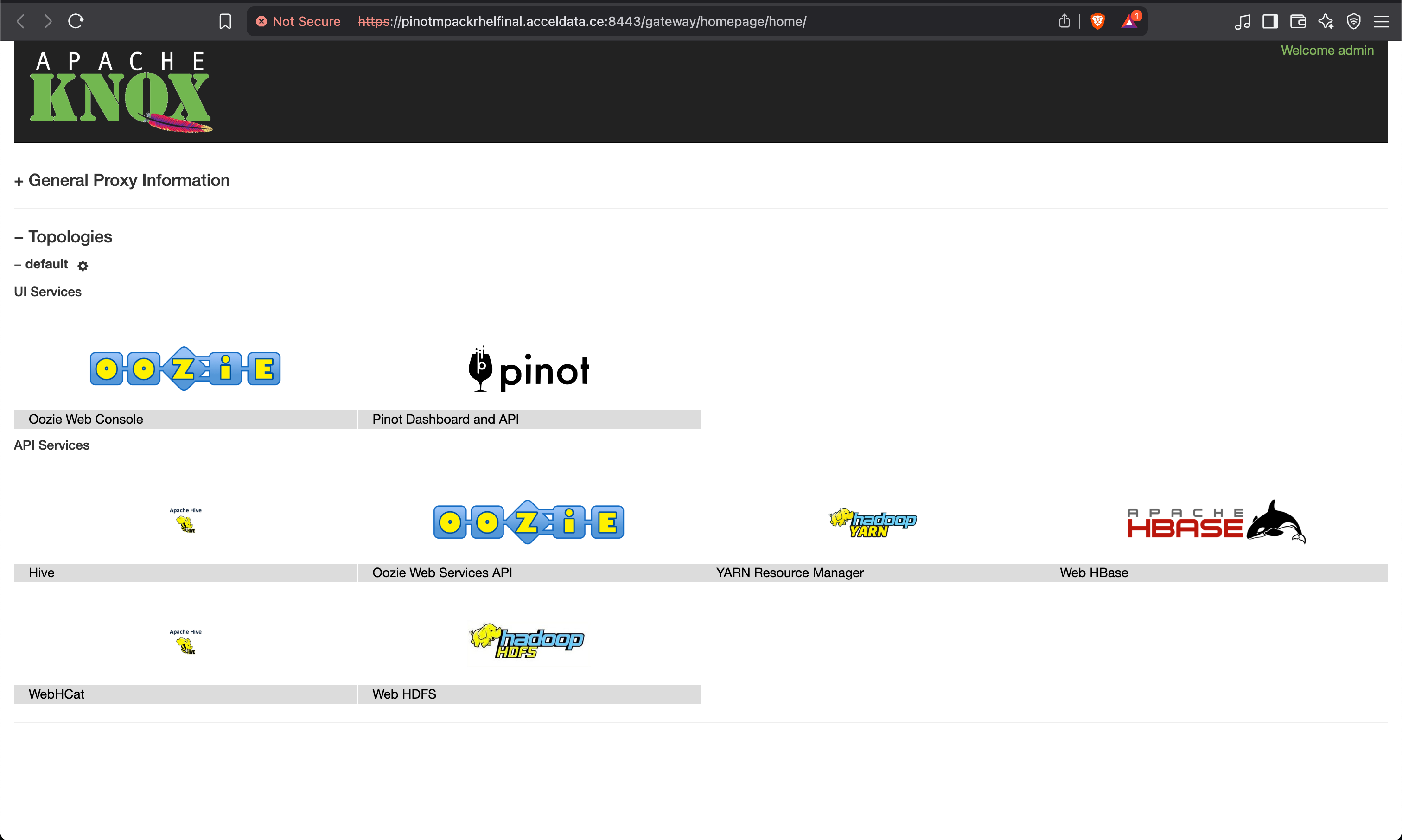
Knox Homepage UI
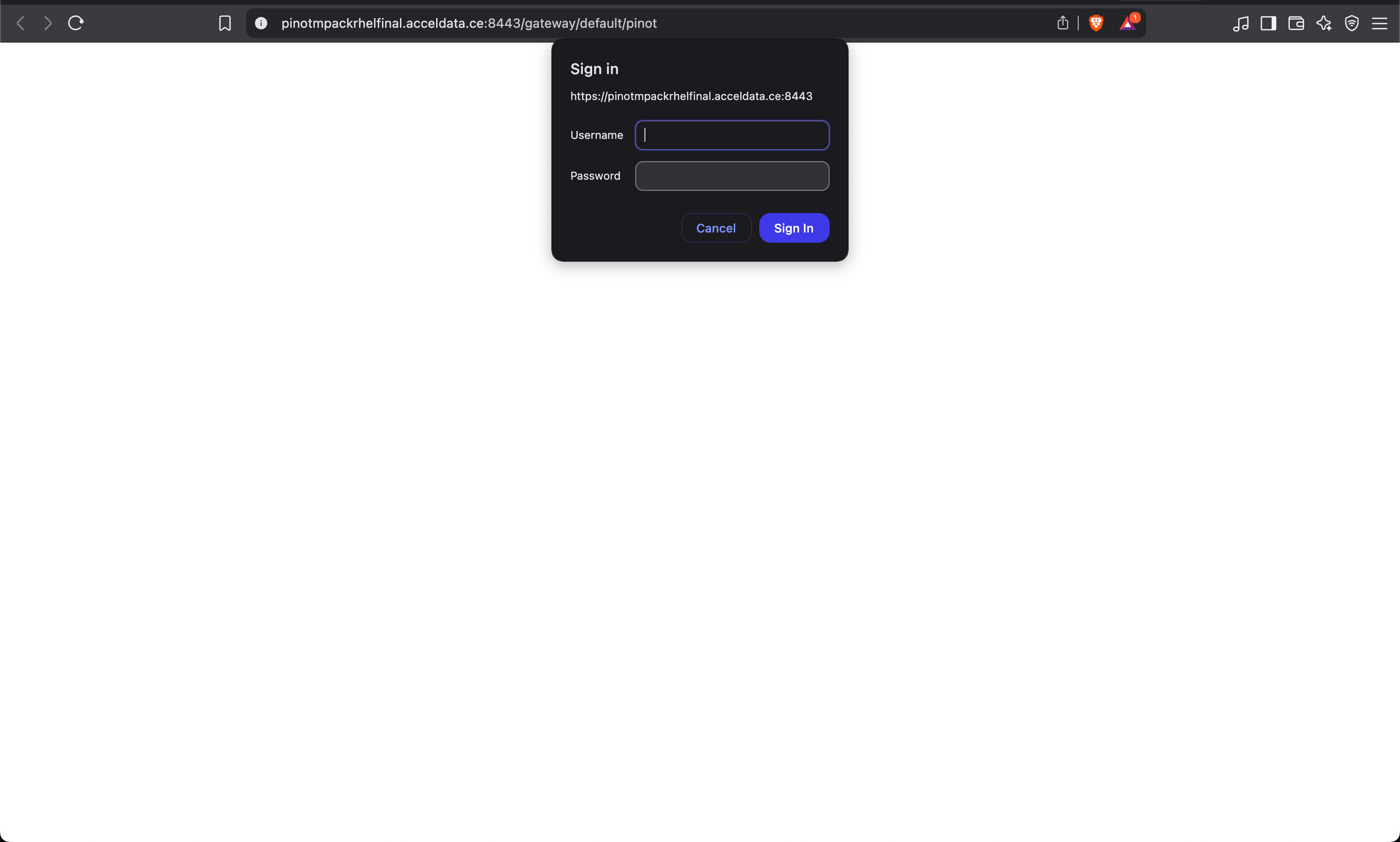
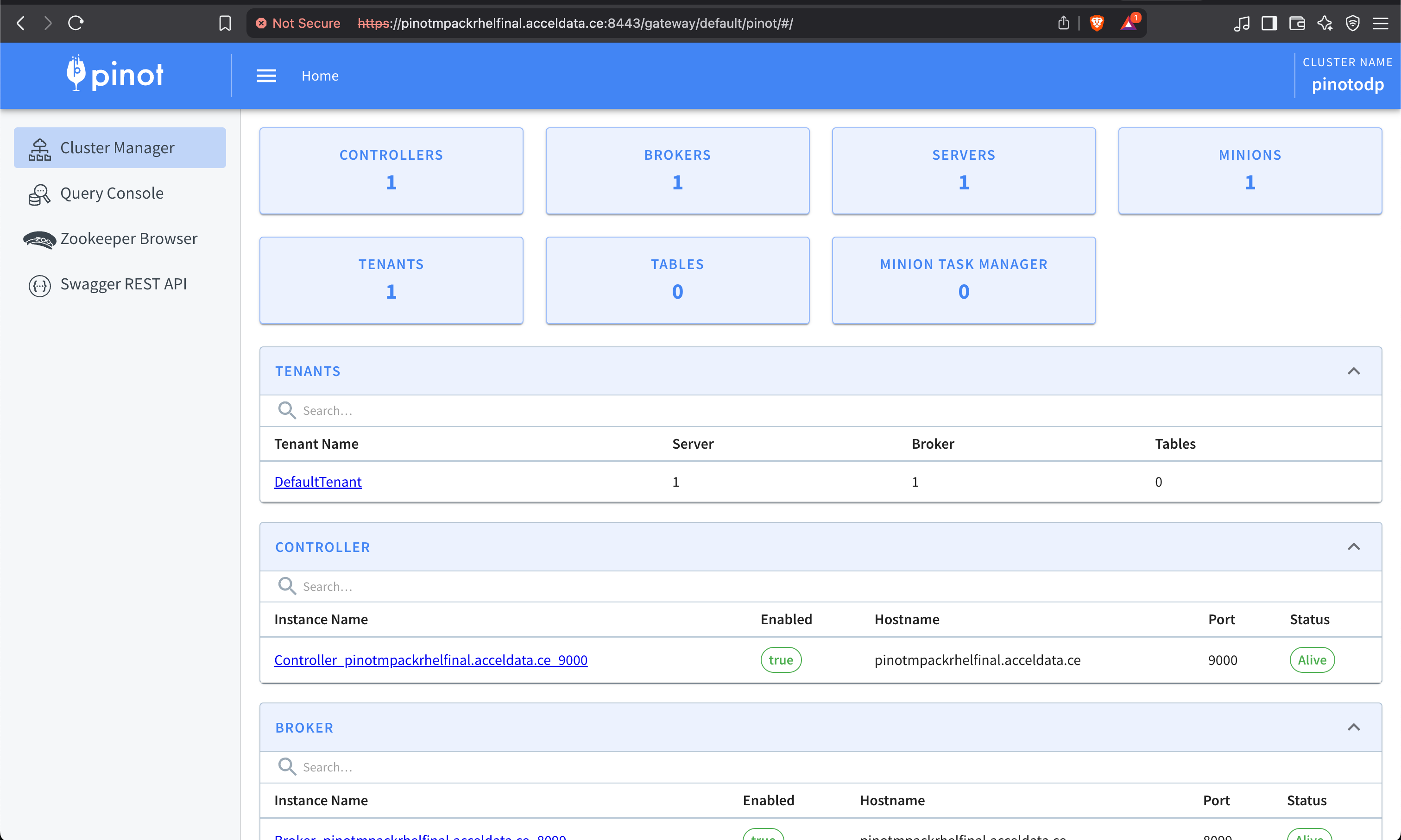
Access the Knox Homepage UI, click the Pinot service, and enter username and password.
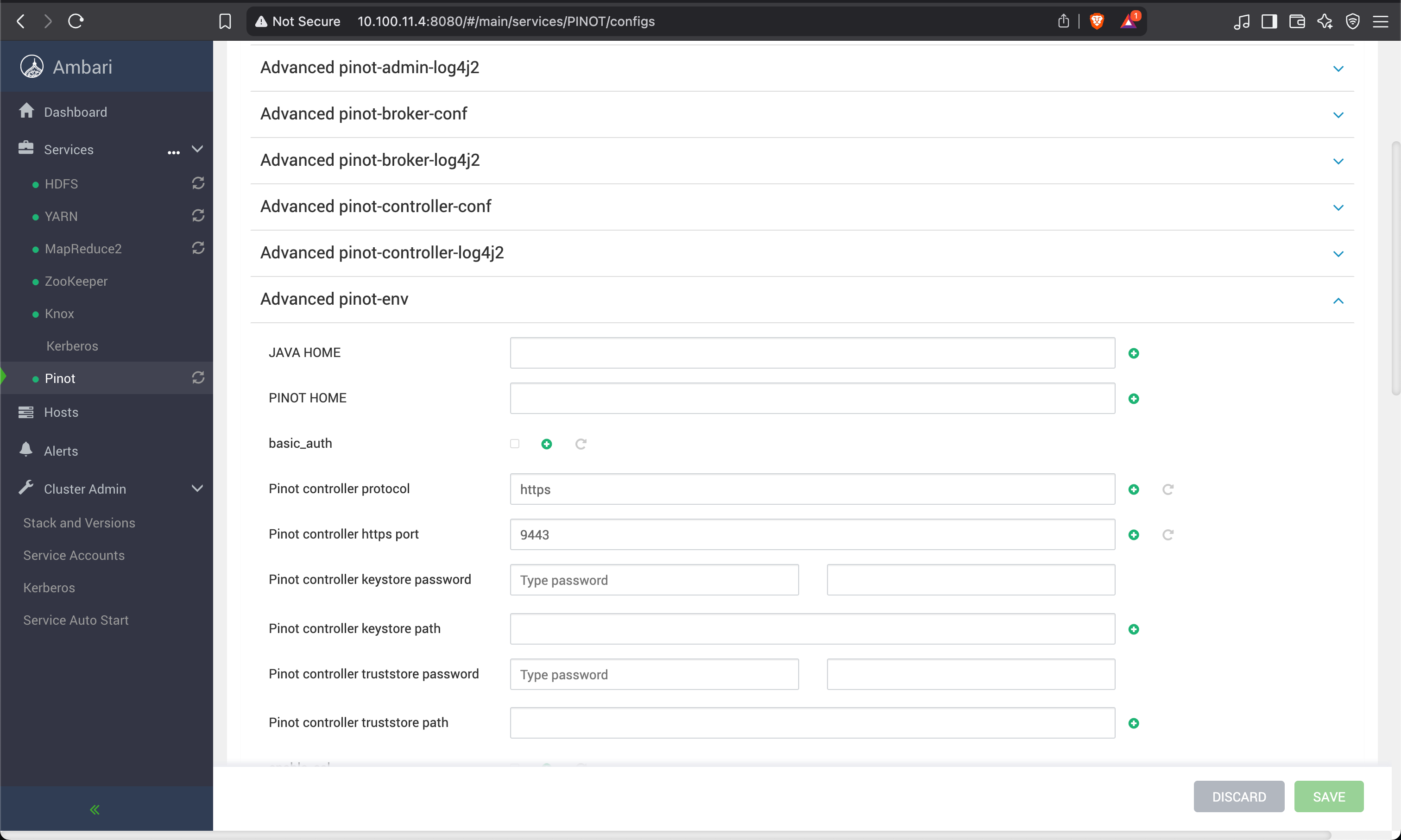
SSL Enablement on the Controller UI
To generate the pinot-keystore.p12 and pinot-truststore.p12 files for securing the Pinot Controller UI using SSL/TLS, follow these steps:
Prerequisites
- Java installed (
keytoolcomes with JDK) - OpenSSL (optional for importing existing certs)
- Directory
/etc/pinot/ssl/exists and has proper permissions
Generate Keystore and Truststore for Pinot Controller
- Generate a Keystore (Self-Signed Certificate)
Bash
xxxxxxxxxxsudo mkdir -p /etc/pinot/ssl keytool -genkeypair \ -alias pinot-controller \ -keyalg RSA \ -keysize 2048 \ -validity 365 \ -keystore /etc/pinot/ssl/pinot-keystore.p12 \ -storetype PKCS12 \ -storepass changeit \ -keypass changeit \ -dname "CN=pinot-controller, OU=Data Platform, O=YourOrg, L=YourCity, ST=YourState, C=US"storepassandkeypasscan be the same.- Replace
CNand other DNAME values as needed.
- Create the Truststore
If you're using self-signed certs, export the public certificate from the keystore and import it into the truststore.
Export certificate from keystore:
Bash
xxxxxxxxxxkeytool -exportcert \ -alias pinot-controller \ -keystore /etc/pinot/ssl/pinot-keystore.p12 \ -storetype PKCS12 \ -storepass changeit \ -file /etc/pinot/ssl/pinot-controller.crtImport into a new truststore
Bash
xxxxxxxxxxkeytool -importcert \ -alias pinot-controller \ -file /etc/pinot/ssl/pinot-controller.crt \ -keystore /etc/pinot/ssl/pinot-truststore.p12 \ -storetype PKCS12 \ -storepass changeit \ -noprompt- Secure Permissions (Optional, but Recommended).
Bash
xxxxxxxxxxsudo chmod 640 /etc/pinot/ssl/*.p12sudo chown pinot:pinot /etc/pinot/ssl/*.p12- Configure Pinot to use the SSL Certificate.
Edit controller.conf or wherever your Pinot Controller properties are set:
Bash
xxxxxxxxxxcontroller.https.port=8443controller.ssl.keyStore.path=/etc/pinot/ssl/pinot-keystore.p12controller.ssl.keyStore.password=changeitcontroller.ssl.trustStore.path=/etc/pinot/ssl/pinot-truststore.p12controller.ssl.trustStore.password=changeitcontroller.ssl.protocol=TLScontroller.ssl.enabled=trueRestart the Pinot Controller after updating the configuration.
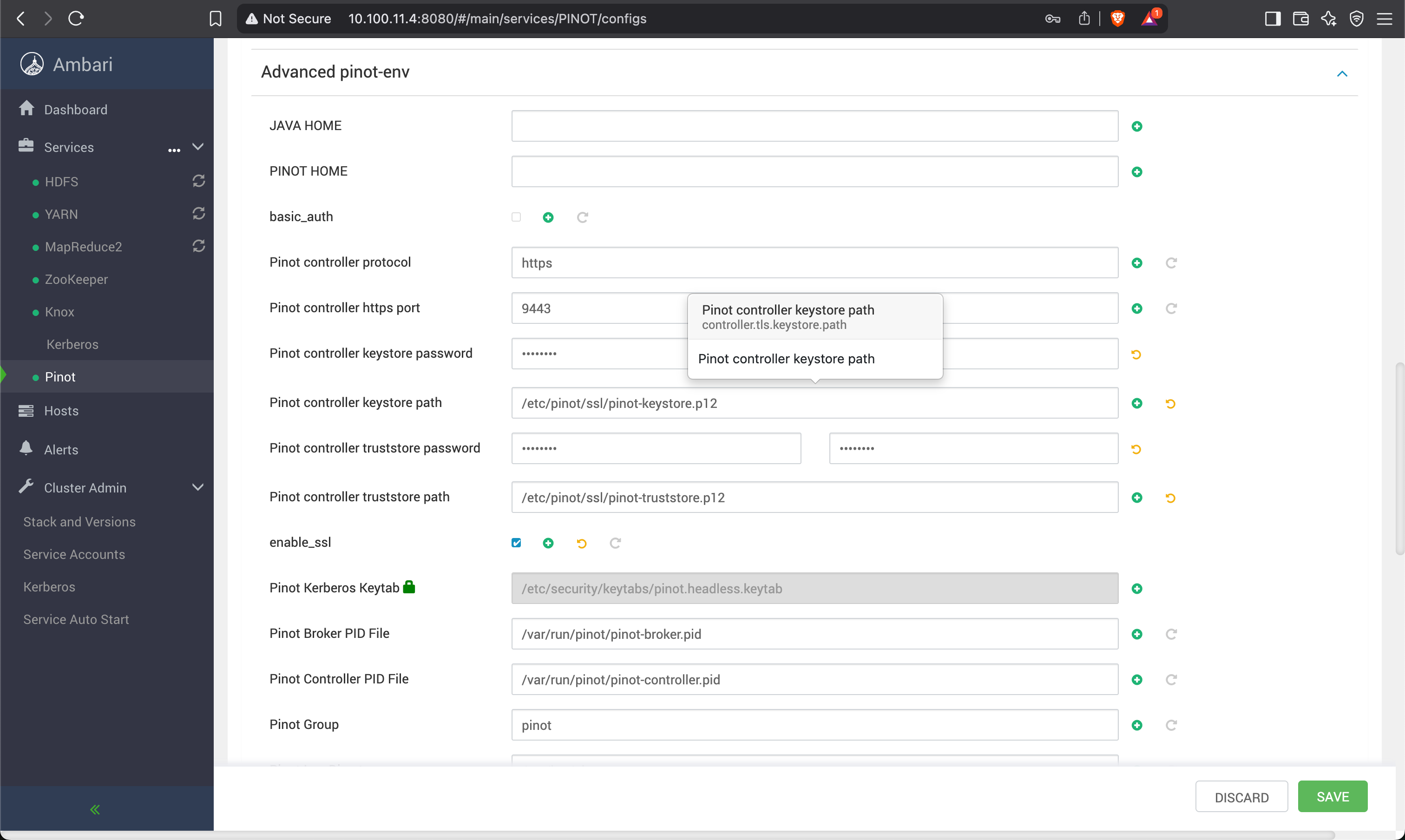
Save and restart the service.
VariableType to search · ESC to discard
GlossaryType to search · ESC to discard
InsertType to search · ESC to discard
No matches
Last updated on May 9, 2025
Was this page helpful?
Next to read:
Batch Import using Local Filenull
Discard Changes
Do you want to discard your current changes and overwrite with the template?
Archive Synced Block
Message
Create new Template
What is this template's title?
Delete Template
Message